Whoa! I fired up my Monero GUI and felt that flicker of curiosity and mistrust. At first glance it looks simple — send, receive, privacy running quietly (oh, and by the way somethin’ about that unsettles me). But my instinct said this was layered; initially I thought knobs were cosmetic, though actually once I dug into ring signatures, decoys, and stealth addresses, a lot of that complexity turned out to be the core privacy engine rather than a shrug-you’re-fine button. Seriously, the GUI eases much of the pain without asking you to understand all the math, and that design choice both helps adoption while sometimes lulling people into thinking privacy is automatic when it’s not.
Hmm… The GUI matters because most users will never touch the command line. I watched new users click through wallet creation and it felt like handing someone a privacy toolbox without warning labels. This matters when you’re trying to avoid linkage across transactions, because small patterns of reuse or timing can let an observer weave together a story from otherwise private-looking pieces. The wallet’s UI choices are therefore not cosmetic; they change behavior.
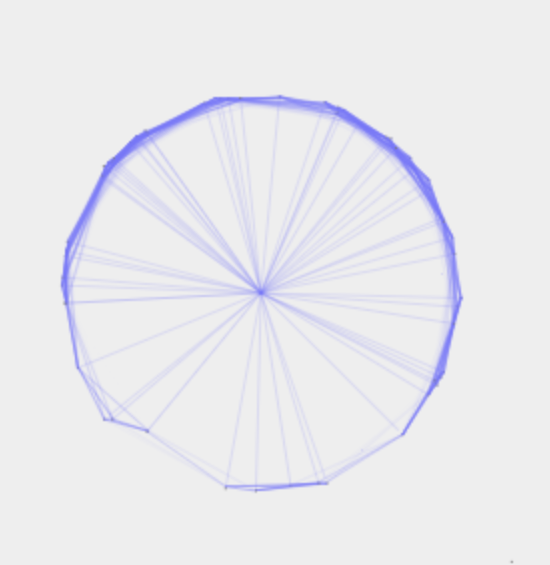
Wow! Ring signatures are the secret sauce that make Monero transactions obscure by mixing your spend with others. Unlike Bitcoin, which points directly from A to B, Monero forms a fog that hides which input is real. Initially I thought the math was just clever theater, but when I traced how decoy selection and the related key image checks interact, I realized the system is deliberately defensive in ways that reward careful design. My instinct said privacy was simple, but when I traced how ring sizes, decoy selection, and timing interplay, that gut feeling shifted into a cautious respect for the subtle math.
Really? Here’s a practical sense of what happens when you use the GUI to send XMR. You pick an amount, the wallet selects decoys, signs with a ring, and crafts a stealth address for the recipient. Conceptually that’s straightforward, yet under the hood there’s a choreography of cryptographic checks that prevent double-spends and reveal nothing about which ring member was the real signer. I won’t give command-line recipes here; think of this as a high-level map rather than a how-to manual.
Whoa! Privacy in practice is a spectrum and user habits move you along it. Opsec choices like address reuse, network isolation, and wallet backups shape actual anonymity. On one hand good software and default ring sizes do most of the heavy lifting, though actually on the other hand human habits, cloud-synced wallet files, or sloppy exchanges can undo privacy in ways that are subtle and heartbreaking — very very avoidable. I’ll be honest — this part bugs me because it’s avoidable; with a few sane defaults and better onboarding most slip-ups melt away before they ever become permanent leaks.
Hmm… I run the GUI on an air-gapped machine sometimes, which is overkill for most, but instructive. You don’t need paranoia to benefit from Monero; sensible defaults go far. Something felt off about some guides that brag about evasion, so I sifted through docs, community posts, and my own mistakes to separate responsible privacy practices from sketchy advice that crosses ethical lines. On the practical side, keep your wallet files backed up and verify addresses carefully.
Wow! The wallet displays confirmations, ring size, and the fee estimate so you can make choices. That transparency is crucial, and the GUI balances it with default safety settings that protect beginners. Initially I thought ‘defaults are enough’ but after watching a few users tweak settings and reveal metadata by mistake I realized defaults reduce risk but don’t remove responsibility. I’m biased, but a little user education baked into the wallet UI, such as clearer warnings and in-context links to concise guides, would prevent a lot of headaches that otherwise land in forum threads later.
Seriously? If you want to learn, check the official resources at monero and try a small test transaction first. On one hand the community values privacy fiercely and provides excellent tooling, though actually you should pair software knowledge with good operational security habits because software can’t compensate for sloppy real-world practices like posting public receipts tied to your identity. A quick tip — separate exchange funds from long-term privacy holdings when possible. In the end I leave you with practical curiosity and a little skepticism; go explore the wallet, respect the tech, and know that privacy is a practice not a checkbox…

Why ring signatures, stealth addresses, and the GUI work together
The GUI is the bridge between cryptographic primitives and everyday users, and ring signatures are one of those primitives doing heavy lifting. Ring signatures obfuscate which input in a set is the true spender without revealing the signer’s identity, while stealth addresses ensure outputs can’t be trivially linked to a public address. When the GUI manages these mechanisms well, most users gain strong privacy without needing to master the math. That said, remember: tooling reduces friction but doesn’t absolve responsibility — your habits finish the story.
FAQ
What is a ring signature in plain terms?
A ring signature mixes your transaction input with other inputs (decoys) so an outside observer cannot tell which one is real; it’s like signing a group card where any participant could have been the signer. The blockchain can still verify the signature’s validity without identifying the real input.
Do I need the GUI to get privacy?
No, but the GUI makes privacy more accessible. For most users the GUI provides sensible defaults that implement ring signatures, stealth addresses, and bulletproofs for confidentiality. Power users can use CLI tools or custom setups, but the GUI lowers the barrier for safe use.
Any simple operational tips?
Yes — avoid address reuse, back up your wallet seed securely, test with small amounts, and be mindful of what you post publicly. Small habits can leak metadata even when the blockchain itself is private.